Sushi Plans To Reimburse Victims Of $3.4M Exploit

Decentralized exchange SushiSwap will soon begin returning funds to users after a faulty smart contract caused over $3.4M of losses over the weekend, but the majority of the stolen assets are yet to be recovered.
On Tuesday, Sushi said roughly $51,000 worth of user assets secured by white-hat hackers would soon be claimable. White-hat hackers exploit code vulnerabilities to secure funds that are at risk of being stolen and typically receive a bounty in exchange for their return.
Sushi said that while funds stolen by malicious “black-hat” hackers are unrecoverable, it’s working on a claim process to make affected users whole. “Our goal is to return all user funds to legitimate claimants,” Sushi said.
On Monday, Sushi’s ‘head chef’ Jared Grey, tweeted that users can again safely trade on Sushi and urged recent users to revoke approvals for the exploited RouteProcessor2 contract.
The incident highlights the importance of maintaining stringent security practices when transacting on-chain. Protocols that are trusted in the community and battle-tested over time can still suffer exploits or ship faulty code.
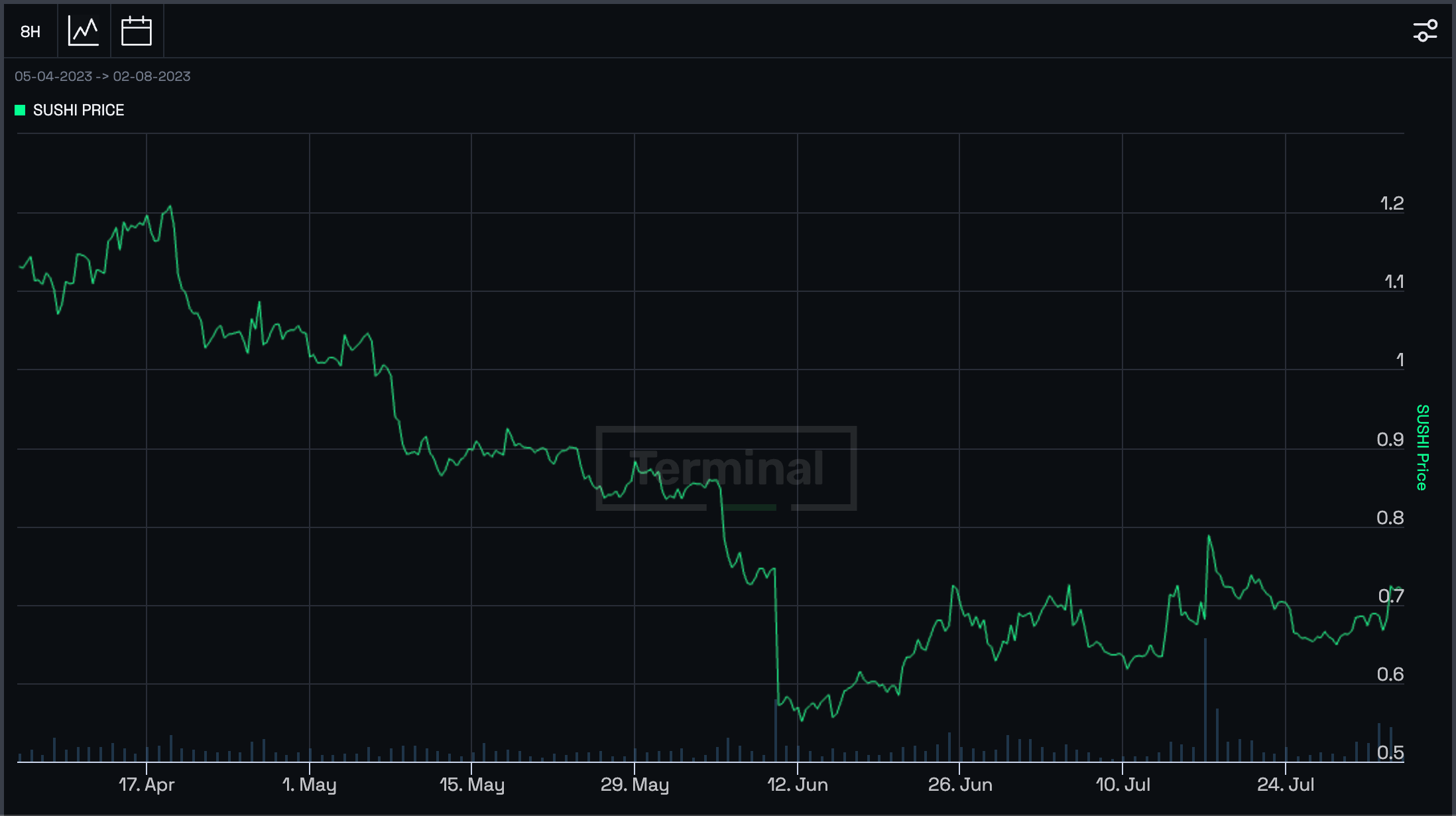
SUSHI fell by more than 5% in the wake of the exploit but has since recovered.
Dodgy Code
PeckShield, a blockchain security firm, identified the exploit on Sunday. It targeted contracts deployed over the preceding ten days, leaving wallets that recently approved Sushi to perform trades vulnerable to attack.
The exploit took advantage of vulnerabilities in Sushi’s recently deployed RouteProcessor2 contract, which users needed to pre-approve to trade ERC-20 tokens on the platform. However, the contract erroneously gave permission for the “pool address” to drain funds approved for trading by unsuspecting Sushi users.
“You likely have no exposure if you haven’t interacted with Sushi in the past ten days, as the exploited contract is less than ten days old,” Sushi said.
Grey said only users who recently traded assets on the exchange were affected by the exploit, emphasizing that liquidity providers are unaffected.
White-Hat Rescue
Trust, a pseudonymous white-hat hacker, was the first to identify the vulnerability. Trust attempted to contact the Sushi team regarding the vulnerability. After failing to hear from Sushi for several hours, Trust attempted to capitalize on the exploit in a bid to beat malicious actors to the punch, stealing 100 ETH from a compromised wallet.
However, Trust said bots programmed to engage in Maximal Extractable Value (MEV) quickly replicated his transactions before he was able to rescue any other assets, making off with $3.4M worth of ETH in the process.
Sifu’s Vision
PeckShield noted that a wallet controlled by Sifu’s Vision, an investment collective managed by 0xSifu, a current adviser to and former CFO of Wonderland, accounted for the majority of the funds stolen with a loss of 1,800 ETH ($3.4M). Grey confirmed the news on Twitter, stating that “most of the notional value of the exploited funds is from one user.”
Trust returned the rescued 100 ETH to 0xSifu.

Wonderland was a member of the Frog Nation DeFi collective, which sought to restructure and take control of Sushi following a messy leadership crisis in late 2021. However, the deal fell apart after 0xSifu was outed as one of the co-founders of the failed Canadian exchange, QuadrigaCX. He was voted out of the project amid the drama but reinstated this January in a governance vote after mobilizing 93% of the votes cast.
On Sunday, Grey said Sushi had recovered 300 ETH, and was in talks with Lido, an Ethereum validator and liquid staking provider, regarding the recovery of an additional 700 ETH.
Advertisement
Get an edge in Crypto with our free daily newsletter
Know what matters in Crypto and Web3 with The Defiant Daily newsletter, Mon to Fri
90k+ Defiers informed every day. Unsubscribe anytime.